John the Ripper is a multi-platform cryptography testing tool that works on Unix, Linux, Windows and MacOS. It allows system administrators and security penetration testers to launch brute force attacks to test the strength of any system password. It can be used to test encryptions such as DES, SHA-1 and many others. Its abilities to change John the Ripper: Password cracking Read More ». Additional modules have extended its ability to include MD4-based password hashes and passwords stored in LDAP, MySQL, and others. Cracking password in Kali Linux using John the Ripper is very straight forward. In this post, I will demonstrate that. John the Ripper is different from tools like Hydra.
Kali linux is one of the biggest distros powered by linux company with around 600 penetration and testing tools
know how to make a kali linux iso live bootable click here.
HOW TO CRACK A PASSWORD PROTECTED ZIP FILE .
fcrackzip is the software preinstalled in kali linuix and backtracks which is used for cracking password by bruteforce attack .
I have created a test zip file name 100.zip with a password of admin for this demonstration purpose .
Go switch to your linux terminal with your zip file and type in the command
fcrackzip -b -c a -l – -u
-b : For bruteforce attack
-c : use charset
-l : specify length
-: minimum to maximum characters you guess the password has
: location of the .zip file .
The example command look like :
fcrackzip -b -c a -l 5-5 -u /root/Desktop/100.zip hit enter
Allow it some time to make the brute force attack
.
you can see the image above it took me around 15 seconds to crack the small password .
As lengthy as the password the time it increases .
After seeing how to compile John the Ripper to use all your computer's processors now we can use it for some tasks that may be useful to digital forensic investigators: getting around passwords. Today we will focus on cracking passwords for ZIP and RAR archive files. Luckily, the JtR community has done most of the hard work for us. For this to work you need to have built the community version of John the Ripper since it has extra utilities for ZIP and RAR files.For this exercise I have created password protected RAR and ZIP files, that each contain two files.
The password for the rar file is 'test1234' and the password for the zip file is 'test4321'.
In the 'run' folder of John the Ripper community version (I am using John-1.7.9-jumbo-7), there are two programs called 'zip2john' and 'rar2john'. Run them against their respective file types to extract the password hashes:
This will give you files that contain the password hashes to be cracked... something like this:
After, that you can run John the Ripper directly on the password hash files:
You should get a message like:
Loaded 1 password hash (PKZIP [32/64]). By using John with no options it will use its default order of cracking modes. See the examples page for more information on modes.Crack Zip Password Kali
Notice, in this case we are not using explicit dictionaries. You could potentially speed the cracking process up if you have an idea what the password may be. If you look at your processor usage, if only one is maxed out, then you did not enable OpenMP when building. If you have a multi-processor system, it will greatly speed up the cracking process. Now sit back and wait for the cracking to finish. On a 64bit quad-core i7 system, without using GPU, and while doing some other CPU-intensive tasks, the password was cracked in 6.5 hours.
Now sit back and wait for the cracking to finish. On a 64bit quad-core i7 system, without using GPU, and while doing some other CPU-intensive tasks, the password was cracked in 6.5 hours. Now if you want to see the cracked passwords give john the following arguments:
Crack Zip Password Kali Linux
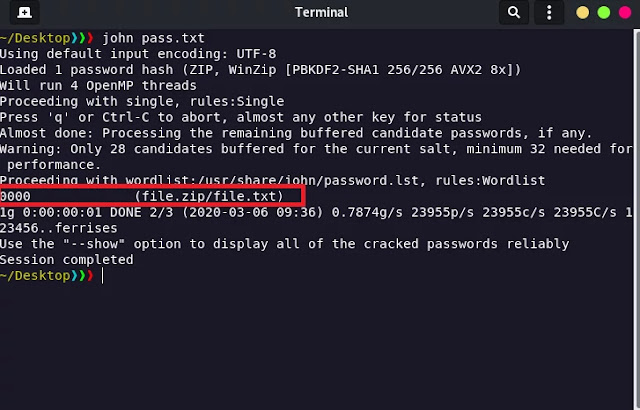
It should output something like:
Note: the hash file should have the same type of hashes. For example, we cannot put the rar AND zip hashes in the same file. But this means you could try to crack more than one zip/rar file at a time.

For the rar file it did not take nearly as long since the password was relatively common. If you take a look at john.conf in the run directory, it has a list of the patterns it checks (in order). The pattern 12345 is much more likely than 54321, so it is checked first resulting in a quick crack.